Safety & Security

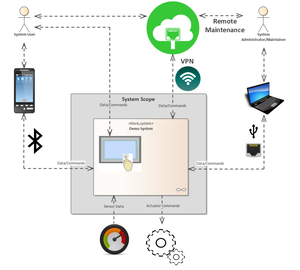
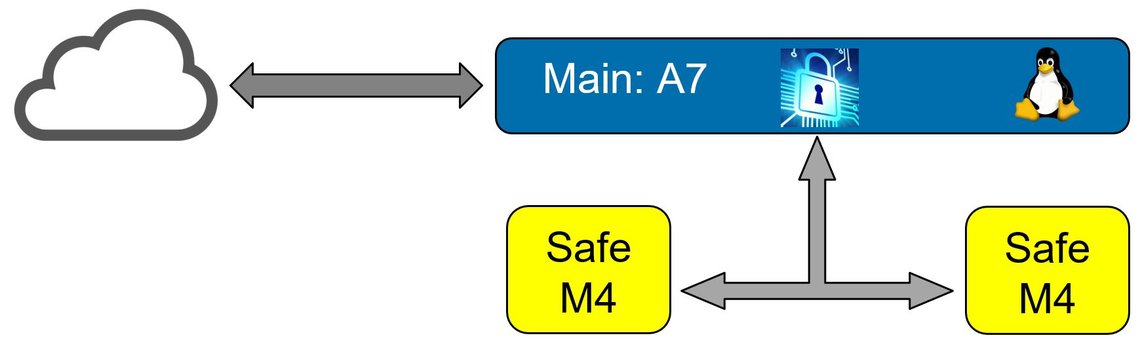
Today, functionally safe products are mostly networked and must therefore be particularly protected against cyber risks due to normative requirements. As a leading development service provider in embedded security and as the first company worldwide whose development process for functionally safe products was certified with the highest maturity level, embeX combines the know-how from both areas in the combination of functional safety and embedded security developing products up to SIL 3 and SL 4 certifications.